In today’s digital world, cybersecurity is no longer a luxury but a necessity. With daily reports of breaches, ransomware, and data leaks, organizations need every available tool to safeguard sensitive information. One of the most effective approaches available is the use of open source intelligence methods (OSINT). These methods help cybersecurity experts gather, analyze, and interpret data from publicly available sources to anticipate threats before they become devastating attacks. In this article, we will explore how OSINT strengthens cyber defense, why it is vital for modern security strategies, and how it influences the future of digital protection.
Understanding open source intelligence methods in cyber defense
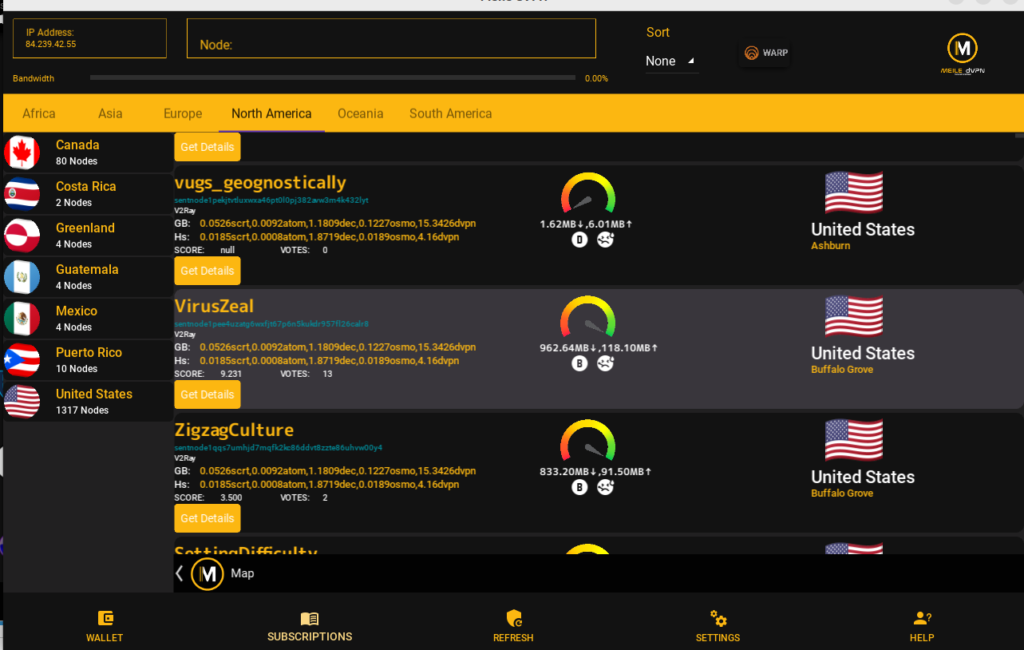
Open source intelligence methods are techniques used to collect, filter, and analyze information from publicly accessible sources. This can include data from websites, forums, social media, government records, domain information, and even the dark web. Unlike private intelligence, OSINT relies on information anyone can access legally without requiring special clearance. This makes OSINT both cost-effective and scalable for organizations of all sizes.
A key reason OSINT is powerful is its ability to gather vast amounts of real-time data. For example, a cybersecurity analyst can monitor leaked credentials posted on underground forums using OSINT tools. By identifying such leaks early, businesses can mitigate risks before threat actors exploit them. This proactive approach makes defense stronger and smarter.
The role of OSINT in cyber defense is also about visibility. Threat actors often leave digital trails across open platforms. By piecing these traces together, cybersecurity teams can develop a clearer understanding of attack patterns, motives, and potential vulnerabilities. It’s like connecting dots on a wide map to spot where danger is coming from.
Cyber defense powered by OSINT doesn’t just look outward at attackers; it also helps organizations look inward. For instance, sensitive company data might be unintentionally exposed on public platforms like code repositories or file-sharing websites. By leveraging OSINT, security teams detect such leaks faster and reduce overall risk exposure.
In addition, OSINT methodologies can complement traditional security measures like firewalls and intrusion detection systems. While these tools defend against known threats, OSINT equips teams with intelligence about evolving threats. This combination enables a more layered, effective cyber defense strategy.
Finally, OSINT gives companies the capacity to anticipate rather than simply respond. By using OSINT proactively, businesses can forecast trends in cybercrime, prepare countermeasures, and even influence security policies. This makes open source intelligence methods an integral part of any modern digital defense program.
Why osint techniques are vital for modern cybersecurity
Cybersecurity today is much more complex than it was a decade ago. Threats come from professional criminal groups, nation-state actors, and even insider threats. Traditional approaches focused heavily on patching systems or reacting after a breach occurs, but these strategies are not enough. This is where OSINT techniques prove their importance.
One major advantage of OSINT in modern cybersecurity is cost efficiency. Since OSINT relies on accessible public data, businesses don’t need large budgets for sophisticated intelligence-gathering tools. Even small organizations can utilize OSINT to detect phishing sites impersonating their brand or unauthorized domains attempting to harvest customer data.
Another reason OSINT is vital is its adaptability. The methods evolve quickly to analyze new platforms, technologies, and online behaviors. For instance, as more businesses migrate operations to the cloud, OSINT providers can monitor misconfigurations in cloud services that could expose sensitive information. This flexibility ensures relevance in a fast-changing digital landscape.
OSINT also supports incident response. When a breach is suspected, OSINT helps investigators trace attackers’ techniques, identify affected systems, and uncover related malicious campaigns. This accelerates incident management and gives organizations a chance to contain the damage before it spreads.
Furthermore, OSINT assists law enforcement and regulatory compliance. Many industries are now required to monitor for external risks and take steps to protect consumer data. OSINT provides audit trails, documentation, and evidence that businesses can use to demonstrate compliance with frameworks such as GDPR or HIPAA.
In addition to corporate security, OSINT techniques also strengthen individual cyber hygiene. Everyday users can benefit from OSINT by monitoring whether their personal email addresses or credentials appear in leaked databases. This aspect of open source intelligence democratizes security, making it accessible to everyone.
How open source intelligence business protects data assets
The open source intelligence business is rapidly expanding because of the value it provides in data asset protection. Enterprises today deal with vast amounts of sensitive data, including customer details, intellectual property, and proprietary algorithms. Safeguarding these assets requires preventive intelligence, and OSINT plays a core role here.
For instance, companies can hire OSINT specialists to actively monitor domains and forums for discussions about stolen databases. By detecting instances of stolen or leaked company data early, an organization can inform stakeholders, revoke compromised credentials, and prevent customer loss. This builds trust with clients and partners.
Another practical example is brand protection. Cybercriminals often set up fake websites, lookalike domains, or phishing campaigns to impersonate legitimate businesses. Open source intelligence methods enable specialists to detect these activities, giving companies the chance to shut them down swiftly. This not only protects customer assets but also preserves brand reputation.
Additionally, OSINT businesses offer threat intelligence solutions that focus on mapping vulnerabilities in the supply chain. Modern cyberattacks often target weaker links within a company’s suppliers or partners. By applying OSINT techniques, organizations can identify threats around vendor exposures and reinforce their overall defense posture.
The open source intelligence business also assists enterprises in proactive policy-making. By regularly analyzing market-wide threat data, companies can adjust their cybersecurity policies to adapt to real trends, not hypothetical risks. This allows them to allocate resources effectively and strengthen their defenses in areas that matter most.
Lastly, OSINT business services integrate with risk management strategies. Enterprise leaders rely heavily on data integrity to make business decisions. With OSINT-based monitoring, they can ensure that crucial data remains uncompromised, undisclosed, and secure from manipulation. Thus, OSINT is not just about security—it’s about maintaining trust and operational continuity.
Practical ways open source intelligence methods expose threats
One of the most practical strengths of open source intelligence methods is their ability to expose emerging threats. Unlike conventional monitoring tools, OSINT can go beyond network boundaries and highlight external risks that directly or indirectly affect an organization.
For example, OSINT tools can scan social media platforms for posts about upcoming attacks or data leaks. Hacktivist groups often announce campaigns publicly before launching them. By detecting these signals early, businesses can prepare their defense mechanisms in advance.
Another effective method is domain and DNS monitoring. Phishing sites typically go live before being used in mass attacks. OSINT platforms can detect domain registrations that mimic legitimate business domains. By flagging these quickly, companies reduce the likelihood of successful phishing attempts.
Dark web monitoring is also a crucial area where OSINT shines. Cybercriminal marketplaces are filled with stolen data, exploits, and hacking tools. When credentials or confidential information related to a company appear on these platforms, OSINT analysts can take proactive measures, such as forcing password resets or alerting law enforcement.
OSINT is equally powerful for identifying software vulnerabilities. Open discussions on forums about unpatched exploits often surface before official advisories. By keeping track of these conversations, organizations can spotlight critical weaknesses and apply fixes ahead of time.
Additionally, OSINT techniques help in understanding attacker behavior. By collecting fragmented data and combining patterns, security teams can map out tactics and predict future moves. This predictive capability transforms cybersecurity from reactive defense into active offense against potential risks.
Future of osint and open source intelligence in cybersecurity
The future of open source intelligence in cybersecurity looks promising, particularly as technology continues to advance. With the growing adoption of AI and machine learning, the ability to process and analyze OSINT at scale will become even more sophisticated. These technologies will allow for real-time threat detection and advanced predictive models that identify risks before any visible attack occurs.
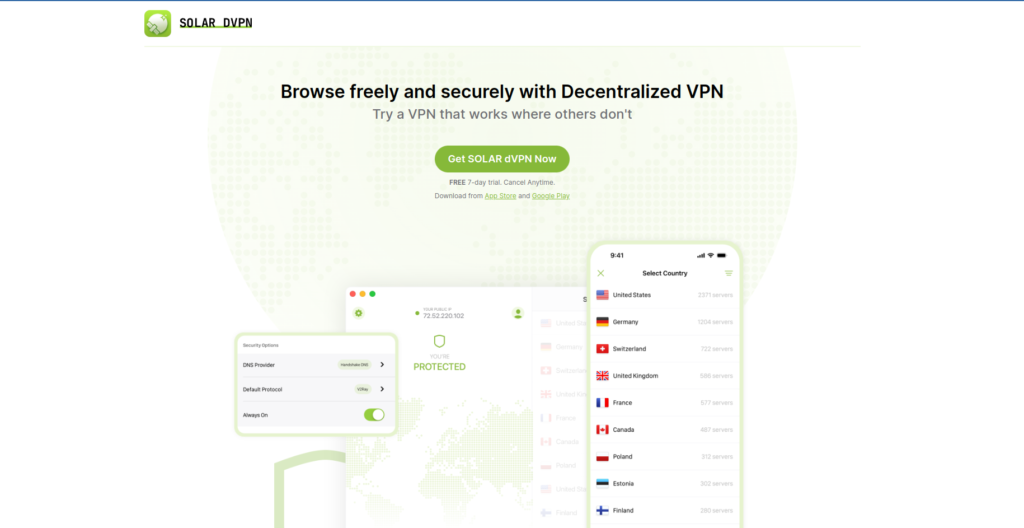
OSINT will also play a critical role in securing IoT devices. As billions of smart devices connect to the internet, new attack surfaces are emerging. Analysts predict that OSINT-based monitoring solutions will be essential in identifying vulnerable IoT endpoints and preventing them from being exploited.
Moreover, collaboration will define the future of OSINT. Governments, private businesses, and security experts are beginning to share intelligence data across networks. This collective defense approach, fueled by OSINT, minimizes blind spots and allows for rapid, united responses to cyberattacks.
Another area of growth will be compliance and regulation. Industries constantly face tighter requirements for data protection. Future OSINT tools are likely to offer automated compliance monitoring features, helping organizations demonstrate adherence to legal frameworks without added overhead.
On a more strategic level, OSINT will become integrated into business decision-making. Boards of directors and executives will rely on OSINT reports to determine corporate strategies, expansion plans, and risk investments. Its value will extend far beyond IT departments, becoming central to organizational resilience.
Finally, with cyber threats becoming increasingly global, the role of OSINT will lean heavily on ethical usage. Responsible practices will become crucial to balancing privacy, legality, and utility. Managed correctly, OSINT will be one of the strongest tools in the future arsenal of cybersecurity defense.
Open source intelligence is a transformative force reshaping how data security is approached. From early detection of phishing websites to proactive dark web monitoring, OSINT provides businesses with visibility and control over emerging digital risks. The open source intelligence business has matured into a cornerstone for protecting sensitive data assets and strengthening brand resilience. As threats evolve and technologies expand, the role of OSINT will only grow more strategic, bridging the gap between knowledge and action. For both individuals and enterprises, embracing OSINT is not a choice—it is a necessity for thriving in the digital age.